You can configure Active Directory Federation Services (AD FS) 2.0 roll-up patch 3 and AD FS 3.0 in the Microsoft Windows Server operating system as your identity provider (IDP) for enterprise logins in Portal for ArcGIS. The configuration process involves two main steps: registering your enterprise IDP with Portal for ArcGIS and registering Portal for ArcGIS with the enterprise IDP.
Required information
Portal for ArcGIS requires certain attribute information to be received from the IDP when a user logs in using enterprise logins. The NameID attribute is mandatory and must be sent by your IDP in the SAML response to make the federation with Portal for ArcGIS work. Since Portal for ArcGIS uses the value of NameID to uniquely identify a named user, it is recommended that you use a constant value that uniquely identifies the user. When a user from the IDP logs in, a new user with the user name NameID will be created by Portal for ArcGIS in its user store. The allowed characters for the value sent by NameID are alphanumeric, _ (underscore), . (dot), and @ (at sign). Any other characters will be escaped to contain underscores in the user name created by Portal for ArcGIS.
Portal for ArcGIS supports inflow of the givenName and email address attributes of the enterprise login from the enterprise IDP. When a user signs in using an enterprise login, and if Portal for ArcGIS receives attributes with the names givenname and email or mail (in any case), Portal for ArcGIS populates the full name and the email address of the user account with the values received from the IDP. It's recommended that you pass in the email address from the enterprise IDP so the user can receive notifications.
Register AD FS as the enterprise IDP with Portal for ArcGIS
- Verify that you are signed in as an administrator of your organization.
- At the top of the site, click Organization and click the Settings tab.
- Click Security on the left side of the page.
- In the Enterprise Logins section, select the One Identity Provider option, click the Set Enterprise Login button, and type your organization's name in the window that appears (for example, City of Redlands). When users access the portal website, this text displays as part of the SAML sign in option (for example, Using your City of Redlands account).
Note:
You can only register one enterprise IDP, or one federation of IDPs, for your portal.
- Choose Automatically or After you add the accounts to the portal to specify how users are able to join the organization. Selecting the first option enables users to sign in to the organization with their enterprise login without any intervention from an administrator. Their account is registered with the organization automatically the first time they sign in. The second option requires the administrator to register the necessary accounts with the organization using a command line utility or sample Python script. Once the accounts have been registered, users will be able to sign in to the organization.
Tip:
It's recommended that you designate at least one enterprise account as an administrator of your portal and demote or delete the initial administrator account. It is also recommended that you disable the Create an account button and sign-up page (signup.html) in the portal website so people cannot create their own accounts. For full instructions, see Configuring a SAML-compliant identity provider with your portal.
- Provide metadata information for the IDP using one of the options below:
- URL—If the URL of AD FS federation metadata is accessible, select this option and enter the URL (for example, https://<adfs-server>/federationmetadata/2007-06/federationmetadata.xml).
Note:
If your enterprise IDP includes a self-signed certificate, you may encounter an error when attempting to specify the HTTPS URL of the metadata. This error occurs because Portal for ArcGIS cannot verify the IDP's self-signed certificate. Alternatively use HTTP in the URL, one of the other options below, or configure your IDP with a trusted certificate.
- File—Choose this option if the URL is not accessible. Download or obtain a copy of the federation metadata file from AD FS and upload the file to Portal for ArcGIS using the File option.
- Parameters—Choose this option if the URL or federation metadata file is not accessible. Enter the values manually and supply the requested parameters: the login URL and the certificate, encoded in the BASE 64 format. Contact your AD FS administrator to obtain these.
- URL—If the URL of AD FS federation metadata is accessible, select this option and enter the URL (for example, https://<adfs-server>/federationmetadata/2007-06/federationmetadata.xml).
- Configure the advanced settings as applicable:
- Encrypt Assertion—Select this option to encrypt the AD FS SAML assertion responses.
- Enable Signed Request—Select this option to have Portal for ArcGIS sign the SAML authentication request sent to AD FS.
- Propagate logout to Identity Provider—Select this option to have Portal for ArcGIS use a logout URL to sign out the user from AD FS. Enter the URL to use in the Logout URL setting. If the IDP requires the logout URL to be signed, Enable Signed Request needs to be checked.
Note:
By default, AD FS requires logout requests to be signed using SHA-256, so you need to check Enable Signed Request and Sign using SHA256.
- Update profiles on sign in—Select this option to have Portal for ArcGIS update users' givenName and email address attributes if they have changed since they last logged in.
- Enable SAML based group membership—Select this option to allow organization members to link specified SAML-based enterprise groups to Portal for ArcGIS groups during the group creation process.
- Logout URL—The IDP URL to use to sign out the currently signed in user.
- Entity ID—Update this value to use a new entity ID to uniquely identify your portal to AD FS.
The Encrypt Assertion and Enable Signed Request settings use the certificate samlcert in the portal keystore. To use a new certificate, delete the samlcert certificate, create a certificate with the same alias (samlcert) following the steps in Import a certificate into the portal, and restart the portal.
Register Portal for ArcGIS as the trusted service provider with AD FS
- Open the AD FS management console.
- Choose Relying Party Trusts > Add Relying Party Trust.
- In the Add Relying Party Trust Wizard, click the Start button.
- For Select Data Source, choose one option for obtaining data about the relying party: import from a URL, import from a file, or enter manually. URL and file options require that you obtain the metadata from your organization. If you don't have access to the metadata URL or file, you can enter the information manually. In some cases, entering the data manually may be the easiest option.
- Import data about the relying party published online or on a local network
This option uses the URL metadata of your Portal for ArcGIS organization. The URL is https://webadaptorhost.domain.com/webadaptorname/sharing/rest/portals/self/sp/metadata?token=<token>, for example, https://samltest.domain.com/arcgis/sharing/rest/portals/self/sp/metadata?token=G6943LMReKj_kqdAVrAiPbpRloAfE1fqp0eVAJ-IChQcV-kv3gW-gBAzWztBEdFY. You can generate a token using https://webadaptorhost.domain.com/webadaptorname/sharing/rest/generateToken. When entering the URL on the Generate Token page, specify the fully qualified domain name of the AD FS server in the Webapp URL field. Selecting any other option, such as IP Address or IP Address of this request's origin, is not supported and may generate an invalid token.
Note:
The arcgis portion of the above sample URL is the default name of the Web Adaptor application. If your Web Adaptor is named something other than arcgis, replace this portion of the URL with the name of your Web Adaptor.
- Import data about the relying party from a file
This option uses a metadata.xml file from your Portal for ArcGIS organization. There are two ways you can get a metadata XML file:
- On the organization page, click the Settings tab and click Security on the left side of the page. Click the Get Service Provider button. This gives the metadata for your organization, which you can save as an XML file on your computer.
- Open the URL of the metadata of your Portal for ArcGIS organization and save as an XML file on your computer. The URL is https://webadaptorhost.domain.com/webadaptorname/sharing/rest/portals/self/sp/metadata?token=<token>, for example, https://samltest.domain.com/arcgis/sharing/rest/portals/self/sp/metadata?token=G6943LMReKj_kqdAVrAiPbpRloAfE1fqp0eVAJ-IChQcV-kv3gW-gBAzWztBEdFY. You can generate a token using https://webadaptorhost.domain.com/webadaptorname/sharing/rest/generateToken. When entering the URL on the
Generate Token page, specify the fully qualified domain name of the AD FS server in the Webapp URL field. Selecting any other option,
such as IP Address or IP Address of this request's
origin, is not supported and may generate an invalid token.
Note:
The arcgis portion of the above sample URLs is the default name of the Web Adaptor application. If your Web Adaptor is named something other than arcgis, replace this portion of the URL with the name of your Web Adaptor.
- Enter data about the relying party manually
With this option, the Add Relying Party Trust Wizard displays additional windows where you enter the data manually. These are explained in steps 6 through 8 below.
- Import data about the relying party published online or on a local network
- For Specify Display Name, enter the display name.
The display name is used to identify the relying party in AD FS. Outside of this, it doesn’t have any meaning. This should be set to either ArcGIS or to the name of the organization within ArcGIS, for example, ArcGIS—SamlTest.
Tip:
If you chose to import the data source from a URL or file, proceed to step 9.
- (Manual data source only) For Choose Profile, choose the AD FS profile that's applicable in your environment.
- (Manual data source only) For Configure URL, check the Enable support for the SAML 2.0 WebSSO protocol box and enter the URL for the relying party SAML 2.0 SSO service.
The relying party URL should be the URL where AD FS sends the SAML response after authenticating the user. This should be an HTTPS URL: https://webadaptorhost.domain.com/webadaptorname/sharing/rest/oauth2/saml/signin.
Note:
The arcgis portion of the above sample URL is the default name of the Web Adaptor application. If your Web Adaptor is named something other than arcgis, replace this portion of the URL with the name of your Web Adaptor.
- (Manual data source only) For Configure Identifiers, enter the URL for the relying party trust identifier.
This should be portal.domain.com.arcgis.
- For Choose Issuance Authorization Rules, choose Permit all users to access this relying party.
- For Ready to Add Trust, review all the settings for the relying party. The metadata URL is only populated if you chose to import the data source from a URL.
Click Next.
Tip:
If the Monitor relying party option is enabled, AD FS will periodically check the federating metadata URL and compare it with the current state of the relying party trust. However, monitoring will fail once the token in the federating metadata URL expires. Failures are recorded in the AD FS event log. To suppress these messages, it is recommended that you disable monitoring or update the token.
- For Finish, check the box to automatically open the Edit Claim Rules dialog box after you click the Close button.
- To set the claim rules, open the Edit Claim Rules wizard and click Add Rule.
- For the Select Rule Template step, select the Send LDAP Attributes as Claims template for the claim rule you want to create. Click Next.
- For the Configure Claim Rule step, follow the instructions below to edit the claims rules.
- For Claim rule name, provide a name for the rule, such as DefaultClaims.
- For Attribute store, select Active Directory.
- For Mapping of LDAP attributes to outgoing claim types, use the following table as a guide to specify how the LDAP attributes will map to the outgoing claim types that will be issued from the rule.
LDAP Attribute Outgoing Claim Type The LDAP attribute that contains the user names (for example, SAM-Account-Name)
NameID Display Name (or a different attribute from the list)
Given Name E-Mail-Addresses
E-Mail Address Token-Groups - Qualified by Domain Name
Group
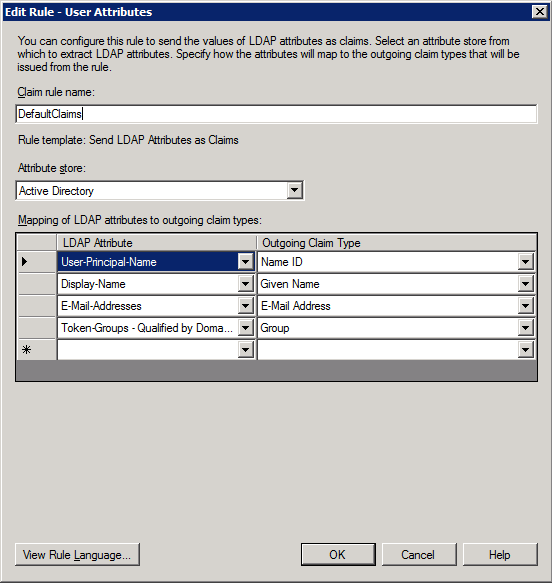
With this claim, AD FS sends attributes with the names givenname and email to Portal for ArcGIS after authenticating the user. Portal for ArcGIS then uses the values received in the givenname and email attributes and populates the full name and the email address of the user account. The values in the group attribute are used to update the user's group membership.
Note:
If you selected the Enable SAML based group membership option when registering AD FS as the enterprise IDP, membership for each user is obtained from the SAML assertion response received from the identity provider every time the user successfully logs in. For information on linking enterprise groups, see Create groups.
- Click Finish to finish configuring the AD FS IDP to include Portal for ArcGIS as a relying party.